Even at these critical moments, there are unfortunately people out there who will try to take advantage of you for their own gain.
Whether you’re a business owner or you’re just trying to protect yourself online, it’s vital you’re aware of potential hackers and scammers, and protected against the rising tide of coronavirus hacking.
We look at some of the known Coronavirus scams going on right now and show you how to avoid hackers during this crisis and how to protect yourself.
Fake pandemic map websites - attempts to steal your sensitive data
Attackers sometimes design these websites to look like official pandemic maps — showing the total number of cases, fatalities and recovered patients in countries and regions. However, they could theoretically take any form, such as news websites.
This is just one of a number of attempts by hackers to lure people into a false sense of security by creating websites that appear trustworthy, but which are ultimately intended to cause harm.
These websites may seem at first to look professional and be well-designed. They may even have relevant URLs, have content that seems trustworthy and relevant, and use up-to-the-minute data to make them seem authoritative.
But when you access a false Coronavirus website, it may force you to try to download an application, claiming it to be an app or dashboard that will help you keep up with breaking news. This, however, is a front: behind the scenes, hackers are using these applications to steal sensitive data from your computer — without you knowing.
How does this scam work?
According to the United State Attorney’s Office at justive.gov, a similar type of scam has also been witnessed taking the form of mobile apps which, once downloaded, will compromise users’ devices and personal information.
How do I protect myself from the fake pandemic map and website scams?
There may be no way to tell if the website you are visiting is legitimate based purely on face value — that’s why it pays to be extra cautious.
The best way to protect yourself from this kind of attack is to be vigilant when browsing the web. Don’t download or install anything on your computer unless you can be absolutely sure of its authenticity.
When downloading apps, only use approved stores like Apple’s App Store and Google Play. Be extra cautious if the app asks you to share sensitive details, such as payment details or location data.
Installing comprehensive anti-virus software on your computer will help to increase your security, as it will vet all downloads, and block installations that it cannot guarantee the security and authenticity of.
Coronavirus phishing emails including malware disguised as attachments
The UK’s National Cyber Security Centre (NCSC) has highlighted a spate of phishing attacks coming from scammers attempting to disguise themselves as legitimate organizations.
They claim that bogus emails may contain links claiming to have important updates which, once clicked, direct users to websites which can attempt to infect devices with viruses, malware and spyware.
The NCSC also mentioned phishing emails being sent to users, which have included infected attachments, such as Word documents. These phishing emails have been seen everywhere from the UK and USA to Japan, Italy and Indonesia.
They have also made attempts to appear highly targeted, the NCSC claim, focusing on specific sectors like shipping, transport and retail in an attempt to lure their victims into a false sense of security.
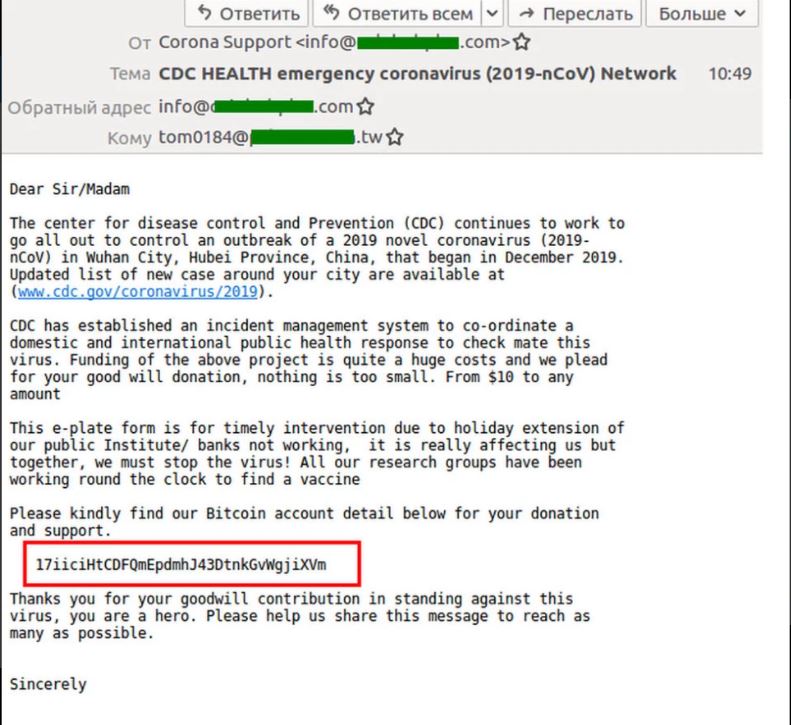
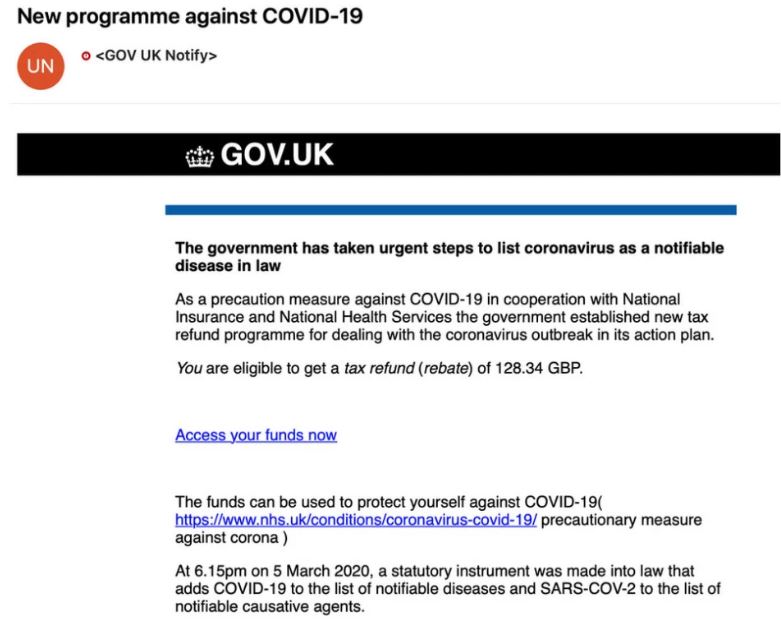
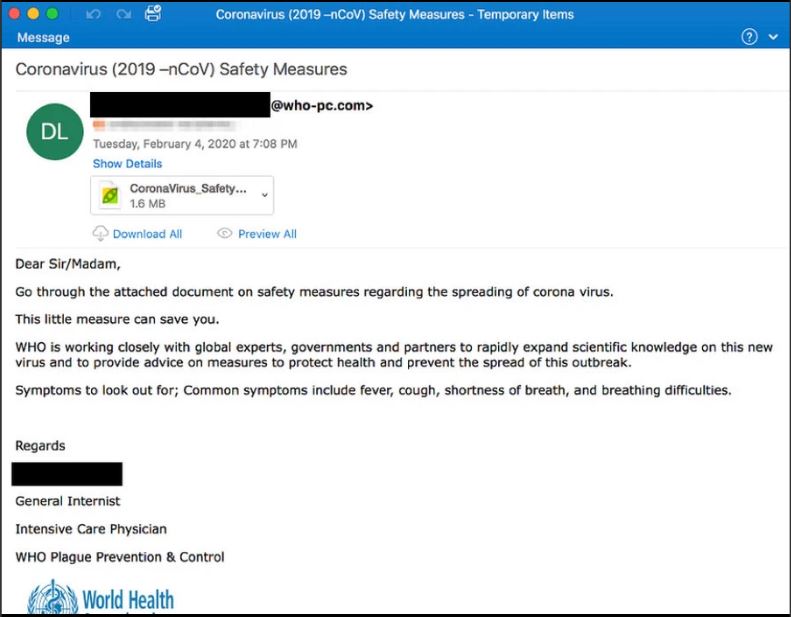
A number of fake and highly targeted Coronavirus phishing emails where the attackers disguise themselves as official organizations including the National Health Center, Centers for Disease Control and Prevention (CDC) and the World Health Organization have also been highlighted.
In one instance, the phishers ask for bitcoin donations to aid the fight-back against the COVID-19 pandemic. In another, they offer to pay the recipient millions of dollars in “compensation” for the effects the Coronavirus is having on their life. And one contains a fake link that redirects to a webmail phish that steals the target’s login credentials.
Finally, the United States Attorney’s Office points out two other types of phishing scams. In one, the recipient is invited to join an investment opportunity, putting their money into publicly traded companies working on equipment that will help to prevent, detect or cure COVID-19. And in another, the senders claim to be working for a hospital which has recently treated a friend or family member of the recipient and asks them to pay the outstanding balance for their treatment.
How does this scam work?
Scammers have attempted to impersonate several authoritative sources, from the World Health Organization (WHO) to state welfare providers.
They may use a number of approaches. Some claim to be selling antiviral equipment. Others request passwords and even bitcoin donations to help fund fake vaccines. Some will ask for the money directly, while others will send a fake or infected link. Some may even include infected attachments with their emails.
Once they have sent users to an infected link, or convinced them to download an attachment, they may use malware such as Lokibot infostealer, Remcos RAT and Emotet banking trojan to steal financial details or hold computer systems to ransom.
How do I protect myself from coronavirus phishing and email scams?
These attacks could take any number of forms, so you should be cautious of any email you receive from a person or organization you don’t know or haven’t subscribed to — even if it appears to be an official body.
When you open an email, check the email address it was sent from. Sometimes, while a person’s name may appear as something official in your inbox — for instance, “World Health Organization” — their email address may not seem as authoritative. For instance, if the email was sent from a regular email provider, such as Gmail, AOL or Yahoo (e.g. “worldhealthorganization@gmail.com”), it’s almost certain this is a fake account.
If you are sent a link, verify the source before you click it. If the website is not the one you are expecting to visit, don’t click. Also, be especially wary of websites that don’t have a Secure Hypertext Transfer Protocol extension — in other words, they should have https:// instead of http:// before their URL.
Lastly, do not download any attachments that you cannot be sure are real or trustworthy. Some email servers allow you to preview a file before downloading it — this is a good way to tell if the attachment is what you think it is.
Furthermore, do not download any attachments that appear to be applications, such as .exe files. These are likely to be viruses, malware or spyware files.
For added security, a comprehensive anti-virus suite could provide extra reassurance, helping to vet email attachments before you open them, in order to prevent hacking and avoid a malware crisis.
Fake online shops and services – selling ‘essential’ coronavirus products
All over the internet, online fraudsters are trying to take advantage of the Coronavirus crisis to trick worried buyers into purchasing products that later turn out to be fake or non-existent.
These scammers have been known to approach frightened users on social media or sometimes directly via email. Many of them claim to have sought-after products such as hand wash, hand sanitizer and face masks. However, when users have gone through and purchased these products, many have found that the products were of low and poor quality — if the products ever arrived at all.
In the US, there have been reported cases of scammers claiming to have Coronavirus tests. These scammers claim to be Medicaid and Medicare representatives with so-called free COVID-19 tests — as long as you pay with a credit card for shipping. Out of fear, several US citizens have already fallen victim to this scam. In response to this (and similar scams hoping to take advantage of the Covid-19 pandemic), the FBI have issued the following statement,
“Look out for phishing emails asking you to verify your personal information in order to receive an economic stimulus check from the government. While talk of economic stimulus checks has been in the news cycle, government agencies are not sending unsolicited emails seeking your private information in order to send you money. Phishing emails may also claim to be related to charitable contributions, general financial relief, airline carrier refunds and fake cures and vaccines”
How does this scam work?
Some fraudsters are disguising themselves as online shops, while others seem to be targeting shoppers via email. Some are even trying to sell their products through social media ads, for instance on Facebook.
It seems they typically focus their attention on medical products which may be in short supply in high street stores and online, such as hand sanitizer, face masks and disposable gloves.
They attempt to lure shoppers in with promises of discounted deals or limited availability. They may also claim to have unique access to stock that other shops can’t get hold of at the moment.
The scammers may ask shoppers to make large purchases on the basis that stockpiling is a necessity. They also attempt to fuel insecurity by making shoppers feel that the products they are selling are in short supply and are selling out fast.
However, once payment is completed, the products will either not show up or, as has happened in Asia (where thousands of people have apparently fallen victim to Coronavirus-related seller scams), will be of much lower quality, or completely different to what was originally promised.
In this, and many other cases, the seller will often disappear soon after the purchase is made, making them impossible to contact and therefore difficult to trace.
How do I protect myself from fake coronavirus ‘shops’ and seller scams?
Start by only buying products from sellers you know and trust. If a seller you don’t know approaches you directly, or if you discover an online store you’ve never seen before, treat it with extreme caution and search for more detail about the seller online to verify their identity. Do not commit to large purchases until you are absolutely sure what you are purchasing is genuine.
If you are buying from a website, check that it has a security certificate — the easiest way to tell is if they have a HTTPS extension (as opposed to the regular HTTP) in their URL.
Most importantly, never give your online passwords or bank details to someone you don’t know or trust. If you need further verification of a seller’s authenticity, they should provide contact details such as an address, company house or company registration number (CRN) and phone number, which you can use to speak to someone in the team.
If you believe you have already fallen victim to a scam, contact your bank immediately. They may be able to provide assistance. Also, be sure to change any passwords you believe may have been compromised during the transaction.

Hackers targeting organizations while staff are working from home
It’s not just individuals who may suffer as a result of coronavirus hacking and scams. Large institutions, including essential healthcare facilities like hospitals, universities and research facilities, are also at risk of coronavirus security breaches.
Earlier this year, Brno University Hospital in the Czech Republic was hit with a ransomware scam that disrupted operations and caused surgeries to be postponed. They haven’t been the only ones either, during this time organizations all over the world have fallen victim to data breaches — even large companies.
Samsung Electronics Co. for example, is believed to have suffered a data breach during the Coronavirus pandemic. However, the extent of breach and exactly who or what was involved remains open to speculation. Reports say the data breach could have been related to a mysterious ‘push notification’ received by some Samsung users. Samsung have claimed that the notifications were unrelated to this potential breach and they claim that the number of people affected were ‘a small number’.
How does this scam work?
Hackers, phishers and scammers often target individual employees with everything from infectious emails to web links, in an attempt to infect their computers. If they are successful, they may be able to gain server access to spread their malware, spyware and viruses across the company.
How do I protect myself from coronavirus hackers targeting me and/or my company?
While your employees are working from home, it’s crucial to remind them of the importance of internet security, and advise them not to open emails, download attachments or click links in emails from people they don’t know or trust.
Your employees are more likely to be distracted at this time, making it easier for hackers to attack when you least expect it. And daily internet usage has increased, meaning the risk is greater for everyone.
There has never been a better or more crucial time to invest in comprehensive anti-virus software for you and your whole organization, to ensure your operations are not disrupted at this vital time.
What are global authorities doing to fight back against Coronavirus scammers, hackers and phishers?
Coronavirus has spread to almost every country worldwide and fighting back against criminals trying to profit from it is something that every country’s government shares responsibility for.
Interpol has been proactive in issuing statements when new Coronavirus scams are brought to their attention.
They have reported on the types of cases they have noticed from around the world. They have also reported that, in some cases, customers have been swindled out of hundreds of thousands of dollars, and that crimes are starting to cross international borders. Meaning you may be just as likely to be targeted by a foreign scam as a local one.
Interpol’s official advice is as follows:
- Independently verify the company/individual offering to sell you any items.
- Be aware of fake websites and note that scammers will often use similar URLs to try to trick you – e.g., abc.org instead of abc.com.
- Read online reviews of a company before making a purchase. If many people claim not to have received their items, the likelihood of a scam is high.
- Be wary of making a payment to a bank account in another country.
- Alert your bank immediately if you believe you’ve been the victim of fraud and gather as much evidence as you can about the details of the transaction(s).
- Do not open attachments or click links you were not expecting to receive.
- Be wary of any unsolicited emails offering to sell you medical equipment or requesting your personal information for medical checks: legitimate health companies typically do not behave in this way.
Interpol claims to have already assisted in at least 30 cases of COVID-19 related fraud in Asia and Europe and has issued a Purple Notice alerting police in all 194 member countries to this new type of fraud.
What are national authorities doing to fight back against Coronavirus scammers, hackers and phishers?
As the entire world has been affected by the Coronavirus, it’s hard to tell what every country is doing to stop the spread of hacking, scamming and phishing in the midst of this crisis.
However, in the USA at least, the Federal Trade Commission (FTC) has stepped in to offer advice to consumers.
They advise:
- Hang up on robocalls. They say scammers may try to pitch Coronavirus treatments or work-at-home schemes over the phone, often using pre-recorded messages.
- Ignore online offers for vaccinations and home testing kits. Only the FDA should be administering these items. So far, no such kits have been approved.
- Fact-check all information. Don’t act on or pass on information if you can’t verify its validity.
- Research online sellers. Make sure they are who they say they are.
- Ignore texts and emails about financial support from the government. You will know the full details of the government aid package when they are communicated via an official channel.
- Don’t click suspicious links or download attachments.
- Watch out for emails claiming to be from official sources. Scammers may try to pose as bodies such as the Centers for Disease Control and Prevention (CDC) and the World Health Organization (WHO). They may also claim to be individual experts.
- Don’t be in a hurry to make donations. Not until you are absolutely sure the person or organization asking for money is genuine and in need.
The FTC also claims that they are actively warning sellers of unapproved and misbranded products, such as teas, essential oils and colloidal silver being marketed as Coronavirus treatments. Be on the look-out for treatments such as these, which sellers may try to plug via social media ads: at the time of writing, there is no approved treatment or cure for Coronavirus, and anyone claiming to have one is only looking to take advantage of you.
What does Kaspersky recommend during this ongoing situation?
At Kaspersky, we’re committed to making sure everyone is safe online. Our malware analyst, Anton Ivanov said this:
“The coronavirus, which is currently hotly debated in the media, has been used as a bait by cybercriminals. So far, we’ve only identified ten unique files, but since this type of activity is common to popular media topics, we expect this number to increase. As people continue to worry about their health, fake documents that are said to educate them about the corona virus may be spreading more and more malware.”
Kaspersky’s recommendations for keeping safe online during the coronavirus pandemic
- Do not open suspicious emails or click on suspicious linksthat promise exclusive Covid-19 content.
- Check file extensions of downloaded files. Documents and video files don’t use the .EXE file format.
- Do not purchase products from unknown or irreputable sources. Do not purchase products from people who don’t know approaching you directly.
- Only obtain information from official, trustworthy sources.
- Protect yourself by ensuring you have reputable antivirus & internet security installed on all your devices.
Related links
Top 6 Online Scams: How to Avoid Becoming a Victim