
Antivirus fundamentals: Viruses, signatures, disinfection
We talk and talk (and talk) about how to behave — and even how to survive — in the digital world. And we hope it’s not in vain, that our
3394 articles

We talk and talk (and talk) about how to behave — and even how to survive — in the digital world. And we hope it’s not in vain, that our

Here on Kaspersky Daily, you can find four detailed articles that explain what exactly a virtual private network (VPN) is and why people use VPNs, describe the different ways to

With lots of the things you buy, it’s easy enough to make an informed decision: read up on car specs, check a banana’s ripeness, try on a jacket. With security

We often advise Android users to download apps from official app stores only. It is much more secure to search for apps on Google Play because all apps in the

In the previous installment of our series about online advertising, we gave a definition of the players involved in digital marketing and a brief description of the payment models used

We’ve talked before about how today’s kids live simultaneously in the real and the digital world. The digital part is important, too — many believe depriving kids of their virtual

Over the past few days, there has been some chatter surrounding Spotify based on a user’s post in the company’s community forum: There’s something pretty alarming going on right now

Fall is update season, at least in the high-tech world. We introduced our new product familyrecently, and Microsoft issued a critical update for Windows 10, aka Redstone 1 or Anniversary

Do you like privacy? Well, let me introduce you to a new player in the encrypted messaging game:Secret Conversations. It comes from a messaging service many are already using, Facebook

Earlier this week, Facebook introduced Marketplace, a service that helps users discover, buy, and sell items locally. Think of it as Facebook’s Groups (which permit the sale of items) meets
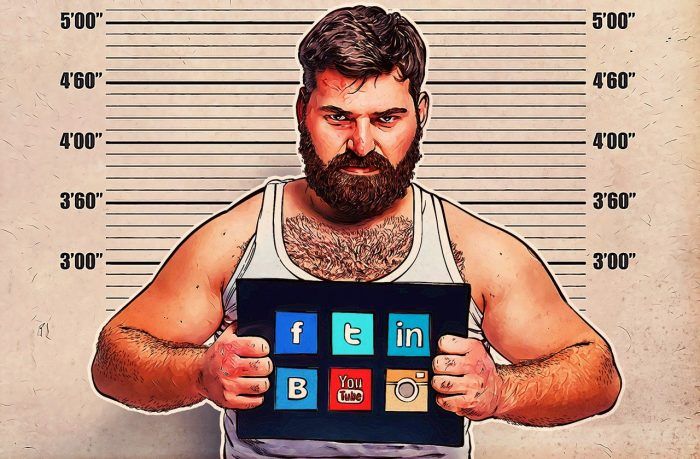
For the most part, we all love social networks — some more than others, of course. Really, how could you not? Social media networks make it unbelievably easy to connect

Every day, new versions and variations of ransomware pop up. Malware creators are still sure that ransomware is their ticket to easy street, despite the fact that law enforcement agencies

Humanity is steadily getting older, which, in turn, increases the number of elderly people online. Today, almost almost 18% of Facebook users are 55 or older. We set out to

We have already told you about a number of hacker groups jackpotting money from ATMs. Now you can see it with your own eyes! Our experts shot four videos of

On August 25, WhatsApp published a blog post detailing its new terms of use. These types of posts rarely generate buzz, but this post detailed end-to-end encryption, exploration of business,

Being a parent is tough in the digital age. The bullies and predators you have to worry about have expanded beyond physical threats to ones that lurk around every corner

Has the shock and awe of Yahoo’s 500 million user credential hack died down yet? Everyone breathing a bit easier? Passwords changed, dead accounts deleted? For those of you chuckling

Danger often comes from an unexpected direction. For example, while you are alert to pickpockets, criminals may be approaching invisibly, over Wi-Fi. Here’s a typical scenario: Let’s say you meet

Some unwanted software announces itself, demanding ransom, tying your computer in knots, crashing the system. By comparison, software that merely installs browser toolbars or other extras, or changes your default

I am not sure about you, but [sarcasm on] my ABSOLUTE FAVORITE THING is opening my mailbox to find unsolicited mail. You know, junk mail [sarcasm off]. Raise your hand

Yahoo is expected to announce a “massive” data breach ahead of its impending sale to Verizon. Although the news is not yet confirmed at the time of this posting (several